Once a security researcher discovers a new strain of malicious software — running a virtual machine on a test-bench — and adds its signature to anti-virus and network monitor blacklists, it's game over. So today's malware devotes enormous energy to figuring out if it's running on a real computer, or inside one of its enemies' virtual worlds.
A presentation from UCSM's professor Giovanni Vigna (who runs the Center for CyberSecurity and Seclab), he's seeing more and more malware that keeps its head down on new infection sites, cautiously probing the operating system to try and determine if it's running on a real computer or if it's a head in a jar, deploying all kinds of tricks to get there.
Ben Rosenbaum and I wrote a Hugo-nominated novella called True Names in which duelling AI superintelligences try to run versions of each other inside virtual environments as part of their overall strategy and tactics.
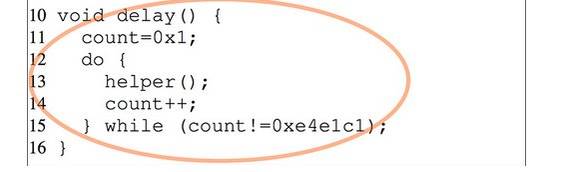
Every system call is a gamble for the malware. Though the compiled binary is far harder to analyse, even when running, than its source code would be, it will still need a good excuse to begin looking up the list of its host system's running processes – in reality seeking out the presence of known analysis tools that might be watching it. Prof. Vigna's own Anubis malware analysis software is on the malware-writer's 'hit list'.Vigna has also found malware source code that specifically seeks out the user 'Andy' in a new environment, as this reflects the name of one of his team in earlier VM battles with malware authors.
Some of this paranoia is contextual – looking up system processes would likely be a red flag in a freeware text editor but merely a routine and expected environment check for a defragger, which would be looking for system elements that may prevent routine system housecleaning.
The malware of the future may come bearing real gifts
[Martin Anderson/The Stack]
(via /.)





