In 2016, EFF sued
the US Government on behalf of Andrew "bunnie" Huang
and Matthew Green, both of whom wanted to engage in normal technological
activities (auditing digital security, editing videos, etc)
that put at risk from Section 1201 of the Digital Millennium
Copyright Act.

Switzerland is about to have a national election with electronic voting, overseen by Swiss Post; e-voting is a terrible idea and the general consensus among security experts who don't work for e-voting vendors is that it shouldn't be attempted, but if you put out an RFP for magic beans, someone will always show up to sell you magic beans, whether or not magic beans exist.

When lawmakers and cops propose banning working cryptography (as they often do in the USA), or ban it outright (as they just did in Australia), they are long on talk about "responsible encryption" and the ability of sufficiently motivated technologists to "figure it out" and very short on how that might work — but after many years, thanks to the UK's spy agency MI5, we have a detailed plan of what this system would look like, and it's called "ghost users."

I have a lot of respect for ex-Microsoft Chief Software Architect Ray Ozzie, but when I saw that he'd taken to promoting a Clipper-Chip-style key escrow system, I was disheartened — I'm a pretty keen observer of these proposals and have spent a lot of time having their problems explained to me by some of the world's leading cryptographers, and this one seemed like it had the same problems as all of those dead letters.

Saleem Rashid is a 15 year old self-taught British programmer who discovered a fatal defect in the Ledger Nano S, an offline cryptocurrency wallet that is marketed as being "tamper-proof."

Ontario Judge Bernd Zabel displayed contempt for his position and its political impartiality by showing up for work the day after the US election in a Donald Trump "Make America Great Again" hat, which he wore, and then perched on his bench.

In July, the Electronic Frontier Foundation filed a federal lawsuit on behalf of Dr Matthew Green, a Johns Hopkins Information Security Institute Assistant Professor of Computer Science; now the US government has asked a court to dismiss Dr Green's claims. A brief from EFF explains what's at stake here: the right of security experts to tell us which computers are vulnerable to attack, and how to make them better.

The Electronic Frontier Foundation has just filed a lawsuit that challenges the Constitutionality of Section 1201 of the DMCA, the "Digital Rights Management" provision of the law, a notoriously overbroad law that bans activities that bypass or weaken copyright access-control systems, including reconfiguring software-enabled devices (making sure your IoT light-socket will accept third-party lightbulbs; tapping into diagnostic info in your car or tractor to allow an independent party to repair it) and reporting security vulnerabilities in these devices.

As part of its big iPhone/iPad launch event today in Cupertino, Apple also released a software update that fixes a flaw which made it possible for iCloud-stored images or video sent via iMessage to be decrypted by third parties. — Read the rest

A paper from some of the most important names in crypto/security history scorchingly condemns plans by the US and UK governments to ban "strong" (e.g. "working") crypto.

Matthew Green's got an excellent postmortem on the huge dump of NSA docs Der Spiegel last weekend.
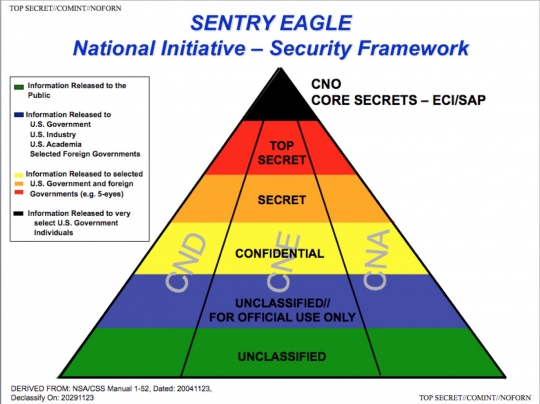
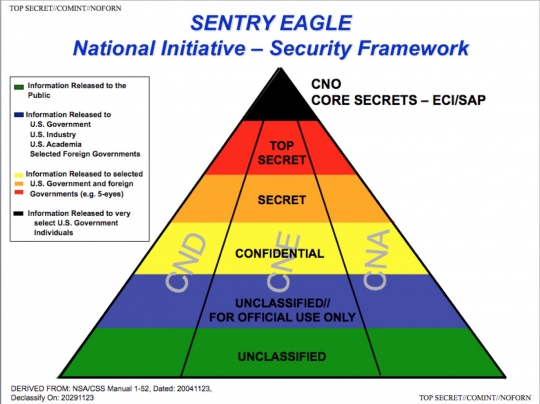
Leaked Snowden documents published by Laura Poitras and Peter Maass in The Intercept describe the NSA's SENTRY EAGLE program describe six programs aimed at weakening the capacity of people all over the world to communicate in private.
 The abrupt announcement that the widely used, anonymously authored disk-encryption tool Truecrypt is insecure and will no longer be maintained shocked the crypto world--after all, this was the tool Edward Snowden himself lectured on at a Cryptoparty in Hawai'i. Cory Doctorow tries to make sense of it all.
The abrupt announcement that the widely used, anonymously authored disk-encryption tool Truecrypt is insecure and will no longer be maintained shocked the crypto world--after all, this was the tool Edward Snowden himself lectured on at a Cryptoparty in Hawai'i. Cory Doctorow tries to make sense of it all.
Joe Menn at Reuters: "A major flaw in Apple Inc software for mobile devices could allow hackers to intercept email and other communications that are meant to be encrypted, the company said on Friday, and experts said Mac computers were even more exposed." — Read the rest

Matthew Green, for The New Yorker:, reports on the challenge of consumer cryptography.
— Read the rest
Over at Dose Nation, my favorite freak writer Erik Davis posts affectionately about Clark Ashton Smith, author of The Hashish Eater (1922) and a host of other weird tales, many for Weird Tales magazine.

When I was a strange young teen, I wrote ornate and old-fashioned poems haunted by images of demons, wizard scrolls, and implacable fortresses.
— Read the rest