A 30-page document containing the master anti-piracy strategy for IFPI (the umbrella group for all the record labels' national associations, like the RIAA and BPI) has leaked. The document, written by IFPI chief anti-piracy officer Mo Ali, has gotten into the hands of TorrentFreak. TorrentFreak's Enigmax summarizes the document in some detail:
Dealing with Internet service providers
In common with cyberlockers, IFPI have a set of rules they'd like to impose on Internet service providers. According to the industry group, ISPs should not provide Internet access to infringing sites, services or even unidentified customers. Furthermore, ISPs are required to "Implement a system of graduated response for infringing P2P users including warnings to an effective deterrent sanction."
Site Blocking
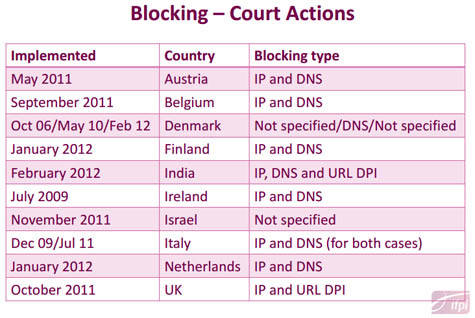
ISPs are also required by IFPI to block access to infringing sites and services "located outside the local jurisdiction." The chart below shows where blocking orders have been obtained (prior to April 2012) and how they are carried out.
Surprisingly, despite reports mounting to the contrary, IFPI seems to think that site blocking is an almost perfect solution to counter infringement.
"The effectiveness of such a 'block' will depend on the determination of the ISP subscriber
and the content/website provider to maintain access to each other and to use circumvention techniques to bypass blocking techniques," they write."There is evidence to suggest that there is limited (between 3% and 5%) adoption of these circumvention techniques although subscribers with more technical knowledge could look to circumvent ISP controls using virtual private networks (VPN) or anonymous proxies."
Leaked Report Reveals Music Industry's Global Anti-Piracy Strategy
(via /.)





